If your website uses a third-party database (such as Senior Systems, Veracross, etc.), you can set whether or not members of a particular role are authenticated against passwords saved in that integrated database, or against passwords saved in Finalsite.
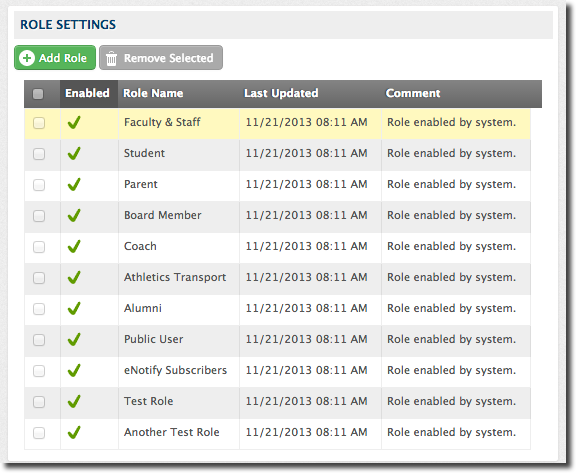
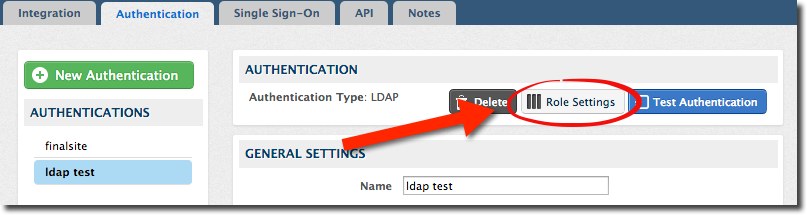
You can go to the “Authentication” tab in the ISM and use the “Role Settings” button there to designate which constituent roles should use the integrated authentication system, and which should use Finalsite's own authentication.
You can temporarily disable the authentication in the event the remote system becomes unavailable. Click on the green check mark next to a role authentication to deactivate it temporarily - the green check mark will turn to a gray 'X'. (The system will display which user last toggled the role authentication.)
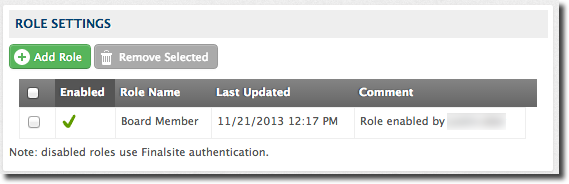
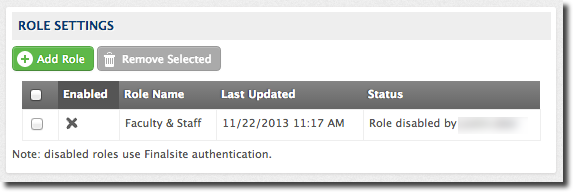
Remote authentications that are disabled will check user passwords against the records stored in Finalsite instead of against those in the specified database. Additionally, any roles not specifically assigned to use a remote system will authenticate to Finalsite by default.
Comments
Please Sign in to leave a comment if you don't see the comment box below.